
Professional Mac antivirus software with hourly malware and adware definition updates.

Disk cleaner, big and duplicate files scanner to save gigabytes of valuable disk space.

Privacy shield that eliminates various information stored when browsing the Internet.

Our support staff is ready to answer all of your questions regarding Combo Cleaner 24/7.

Real-time anti-malware scanner defends your PC from the latest malware threats.

Big and duplicate files finder can uncover and save gigabytes of valuable disk space.

Real-time anti-malware and specific folder protection modules will keep your photos and documents protected from ransomware attacks.

Our support staff is ready to answer all of your questions regarding Combo Cleaner 24/7.

Powerful anti-malware with web browsing protection.

Removes obsolete and useless files that clutter your device.

Total control of notifications and running apps.

Our support staff is ready to answer all of your questions regarding Combo Cleaner 24/7.
Blocks scams, phishing, rogue websites, and malicious downloads.
Check if your email was compromised in an online breach.
Protects you from malicious links in messages and calendars.
Encrypts your Internet traffic and hides your location.
Features
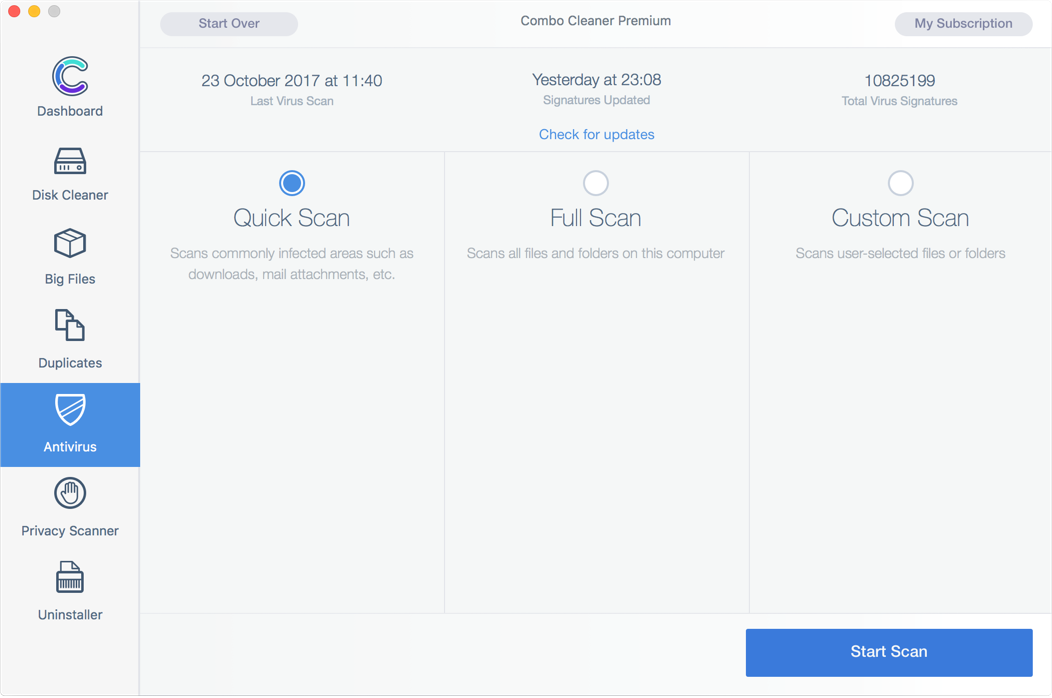
Combo Cleaner is equipped with award winning virus, malware, and adware scan engines. Free Antivirus scanner checks if your computer is infected. To remove infections, you will have to purchase the full version of Combo Cleaner.
Our antivirus software is specifically designed to fight Mac native malicious applications, however, it also detects and lists PC related malware. The virus definition database is updated hourly to ensure that you are protected from the latest outbreaking malware threats

No more pop-ups or unwanted ads while browsing the Internet

A dedicated malware research team works 24/7 to ensure Combo Cleaner users are protected from outbreaking malware threats.

Combo Cleaner Antivirus is equipped with an extensive database of PC threats to prevent you from inadvertently sending malicious files to your friends and other PC users.
Features
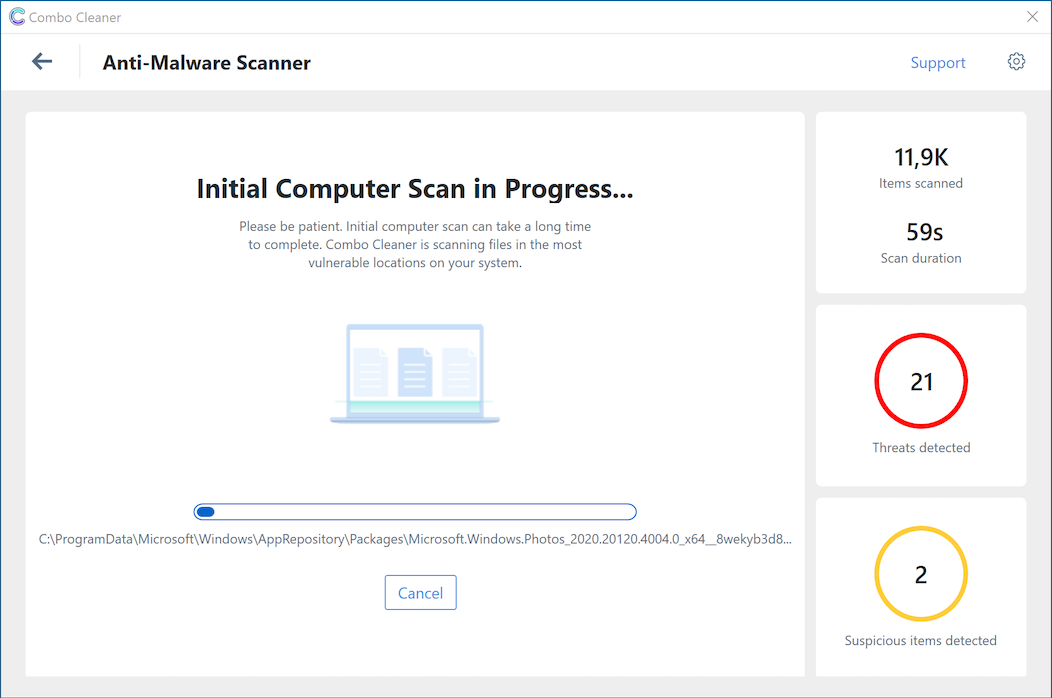
Combo Cleaner anti-malware capabilities consist of four main modules. Powerful on-demand scanner that will scan every file on your computer for malicious code. Real-time anti-malware scanner will uncover malicious applications the second they are being downloaded or executed. Anti-ransomware module will protect your selected folders from file encrypting malware. Web-protection module will prevent you from visiting phishing and infected websites.
Our anti-malware modules are created by security professional who actively track latest malware families and update Combo Cleaner accordingly so that our users get the best protection.

Scan every file on your computer to be sure no malware is active on your PC.

Combo Cleaner will check every file that you download, every email that you receive and will warn you about possible malware infections.

Additional protection layer that let's you choose folders that will be rigorously protected from any malicious file encryption attempts.
Features
Combo Cleaner - Phone Cleaner is equipped with professional anti-malware scan engines that protect your device from spyware, trojans, ransomware, and adware.
Using our application, you will be sure that your device is malware free. Moreover, we will protect your Internet browsing by blocking malicious, phishing, and scam websites. We will also remove spam Chrome notifications that you might unwillingly allow.

Scans your device and removes any currently present malware, spyware, and trojans.

Checks downloaded files and applications, ensuring no malicious code is present on your device.

Monitors your online browsing and protects you from entering malicious websites.

Features
Web Protection - Combo Cleaner will protect your Internet browsing from scams, phishing, malicious downloads, and rogue websites.
Password Checker - check if your password is strong and not easily hackable. This feature will also check the online breaches database and advise if your password is safe.

Extra security layer for your Internet browsing.

Make sure your password is not easily hackable.

Disk Cleaner ensures that your Mac is free of junk and obsolete files that can accumulate megabytes of wasted disk space. Disk Cleaner is free to use.
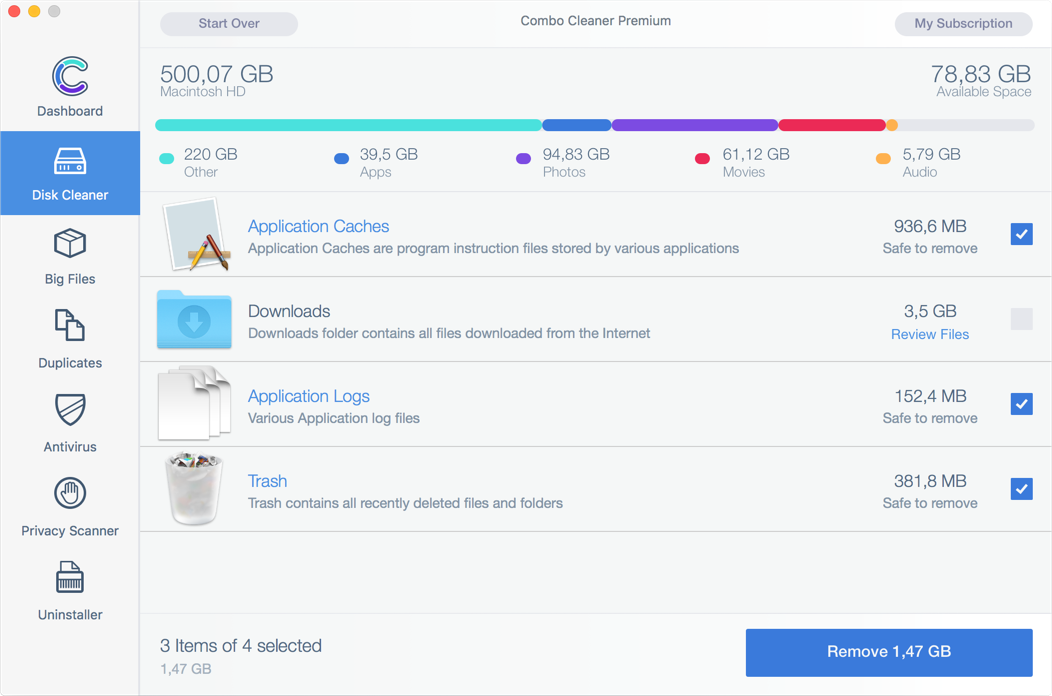

Eliminate all Junk Files
Combo Cleaner’s disk cleaner utilizes a robust scan algorithm, which momentarily checks your hard drive for junk and various temporary files. After a quick scan, you are presented with a concise list of application cache, logs, browser data, and other useless files that can be safely removed to regain valuable disk space. This utility alone can save you gigabytes of disk space, and the best part: it is totally free.

Smart Scan
Fast and powerful “smart scan” algorithm. With just one click you will be able to clean application caches, downloads, application logs, trash, and other obsolete files.

External Hard Drives
Combo Cleaner is capable of scanning your external hard drives for duplicate and junk files. This feature is extremely useful for cleaning hard drives used for backups and storing data.
Running out of storage space? Combo Cleaner - Phone Cleaner has three dedicated features that will help you regain valuable storage space. Using Combo Cleaner, you can easily remove duplicate and bad-quality photos, eliminate hidden cache and uninstall apps you rarely use.


Cleaner
Checks your device for thumbnails, empty folders, hidden cache, and other unnecessary files to reclaim disk space.

App Uninstaller
Conveniently displays all your installed apps in one place. Allows distinguishing rarely used and large applications.

Photo Cleaner
Scans your media and displays photos that are duplicate, old, or have quality/brightness issues.
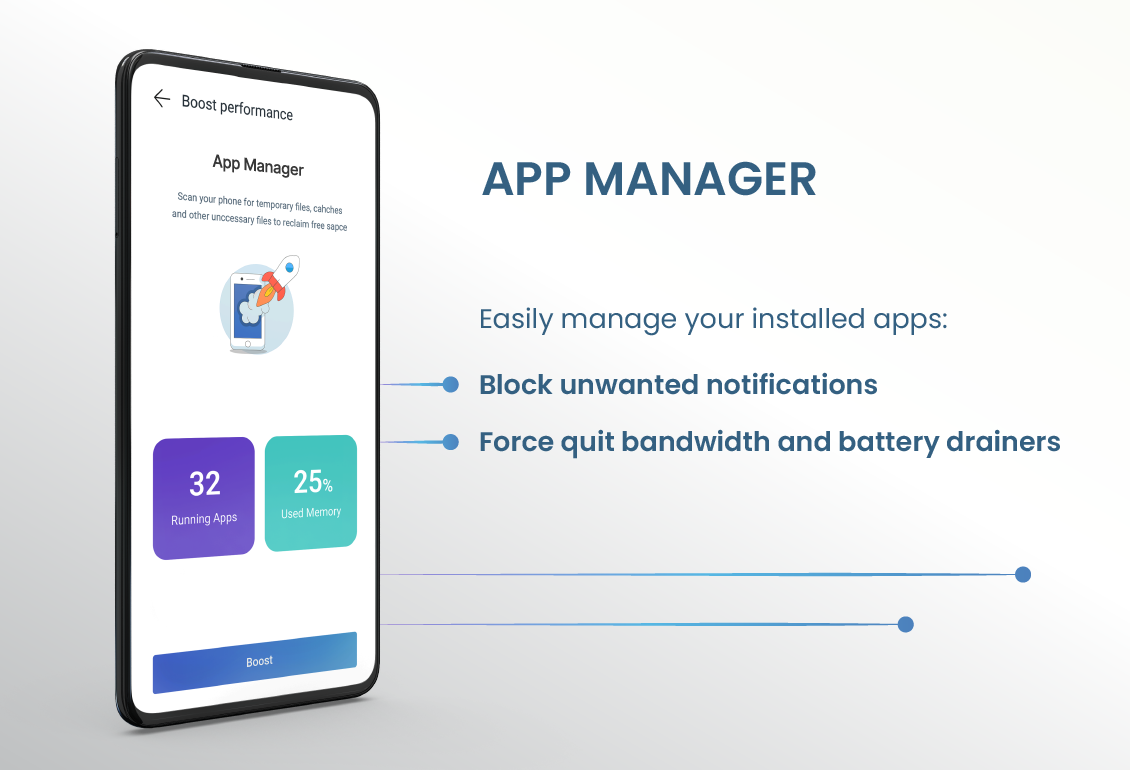
Allows to discover and close apps that drain the most battery and use the most bandwidth. The notifications monitor allows spotting apps that show most notifications and enables you to block them effortlessly.

Displays apps that show most notifications and allows blocking them effortlessly.

Lists apps that drain device battery the most and allows you to close them easily.

Shows applications that use most Internet data and allows convenient closure of them.
Online service breaches happen all the time. Our Identity Protection feature allows you to assess if your personal data has been exposed.
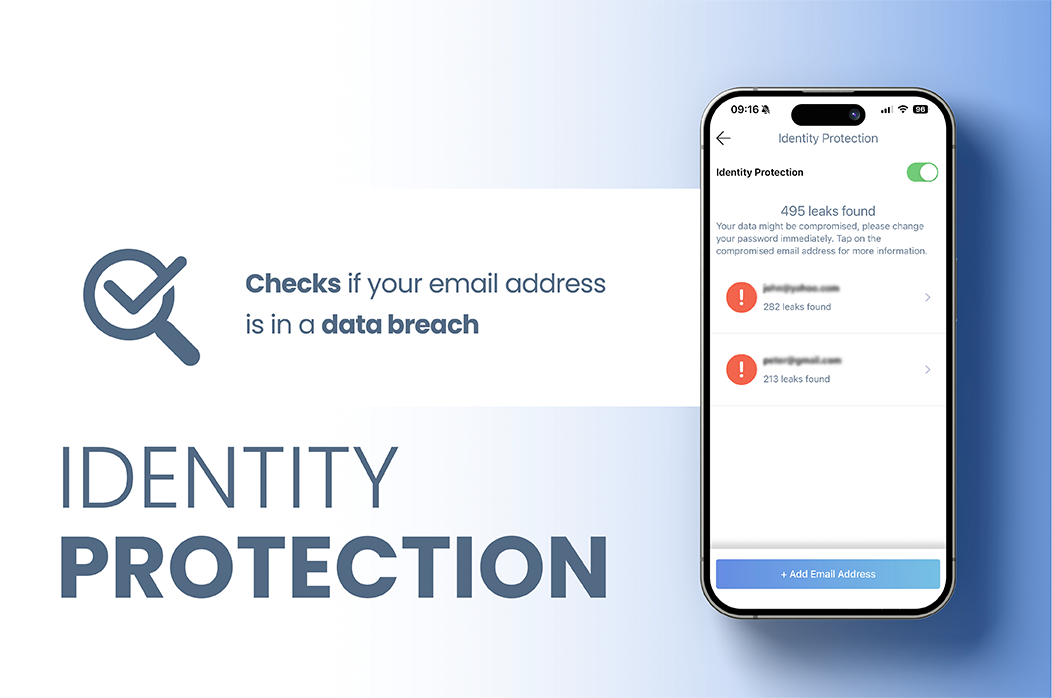

Breach checker
Easily check if your data was exposed in a breach.

Management
Look through the potential breaches and change your password.
SMS messages and Calendar invites can contain malicious links. They can lead to scams and phishing attempts. Combo Cleaner scans and blocks such links, protecting you from visiting malicious websites.

Filters SMS messages that contain malicious links.

Scans calendar events and notifies about rogue links.

Are you taking a lot of photos? Keep your album neat and organized with photo cleaner.


Similar Photos
Quickly identify and remove similar photos.

Bad quality, brightness issues, and old photos
Look through your photos and remove the ones with quality issues.
Protect your privacy while browsing the Internet. Our VPN encrypts your traffic and hides your IP.

Your online traffic is hidden even on public networks.

Your IP address is hidden, and you can change your virtual location to another country.

Application Caches
Application Caches are program instruction…

Downloads
Downloads folder contains all files downloaded...

Application Logs
Various Application log files

Trash
Trash contains all recently deleted files and folders
Duplicate files are identical copies stored in various places on your hard drive. These files are a waste of valuable disk space. Duplicate files scanner is free to use.
Combo Cleaner locates junk file duplicates and lists them in an easily-understood form. Removing duplicate files has many benefits. For example: recovering wasted disk space, reducing file search times, minimising media backup times, etc.

Support for Many File Formats
Combo Cleaner finds duplicate songs (with associated audio files), documents, photos, MP3 files, videos, and more. Removes duplicate folders.

Finds Duplicate Files on Local and External Hard Drives
Combo Cleaner locates duplicate files and lists them in an easy-to-understand form. Removing duplicate files has many benefits. For example: recovering wasted disk space, reducing file search times, minimizing media backup times, etc.

Fast and Precise Detection
Fast, precise detection of duplicates by analyzing file content and attributes. Combo Cleaner’s Duplicate Files Finder analyzes individual file data to locate similar matches.
Duplicate files are identical copies stored in various places on your hard drive. These files are a waste of valuable disk space. Duplicate files scanner is free to use.
Combo Cleaner locates junk file duplicates and lists them in an easily-understood form. Removing duplicate files has many benefits. For example: recovering wasted disk space, reducing file search times, minimising media backup times, etc.

Support for Many File Formats
Combo Cleaner finds duplicate songs (with associated audio files), documents, photos, MP3 files, videos, and more. Removes duplicate folders.

Finds Duplicate Files on Local and External Hard Drives
Combo Cleaner locates duplicate files and lists them in an easy-to-understand form. Removing duplicate files has many benefits. For example: recovering wasted disk space, reducing file search times, minimizing media backup times, etc.

Fast and Precise Detection
Fast, precise detection of duplicates by analyzing file content and attributes. Combo Cleaner’s Duplicate Files Finder analyzes individual file data to locate similar matches.
Privacy Scanner scans system and installed browsers for private data and enables you to easily remove stored browsing history, cookies, etc. To remove detected items you will have to purchase the full version of Combo Cleaner.
Cookies are files created on your system when browsing various sites. They are used to keep track of your movement within websites. Browsing history files contain information pertaining to websites you have visited, information entered into forms, etc. Cache files contain copies of your frequently-visited websites. In the wrong hands, this information can compromise your privacy.

Messages
2 items, 134,7 MB available for removal

Safari
11 items, 21,6 MB available for removal

Google Chrome
9 items, 702,1 MB available for removal

3 items, 779,3 MB available for removal

Full reset
3 items, 1,39 GB available for removal

Mozilla Firefox
10 items, 41 MB available for removal

Privacy Guard
Enables you to eliminate various information stored when browsing the Internet, including cookies, history, cache, and other files that can reveal your private information.

Improves Performance
Removal of the these files also improves Internet browser performance. Combo Cleaner supports all major Internet Browsers (Safari, Google Chrome, Mozilla Firefox, and Opera).
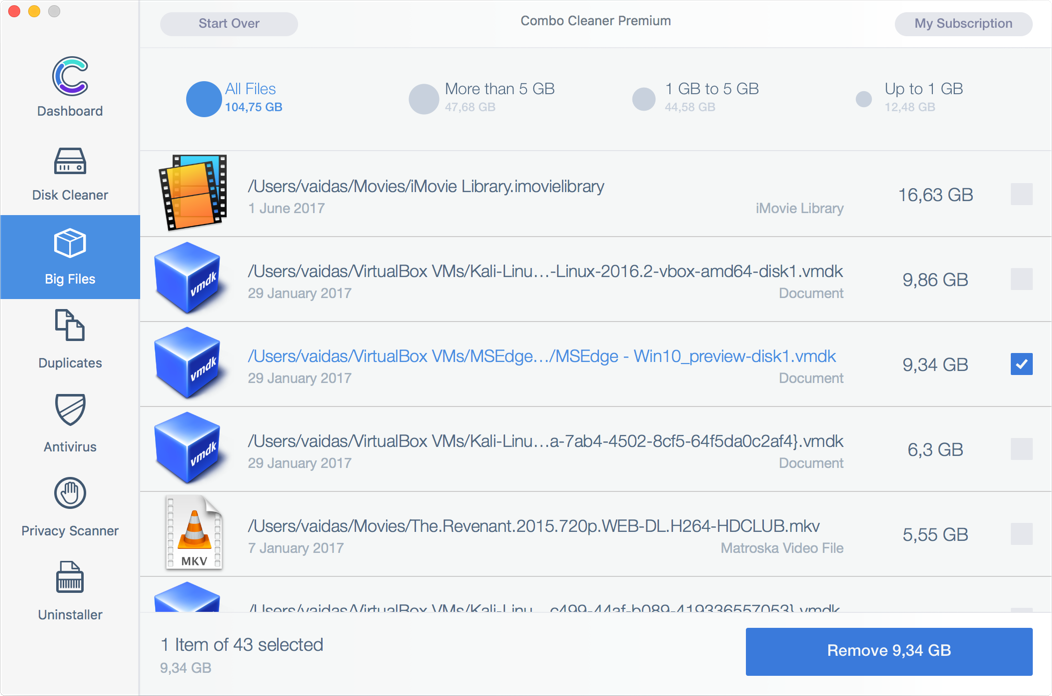
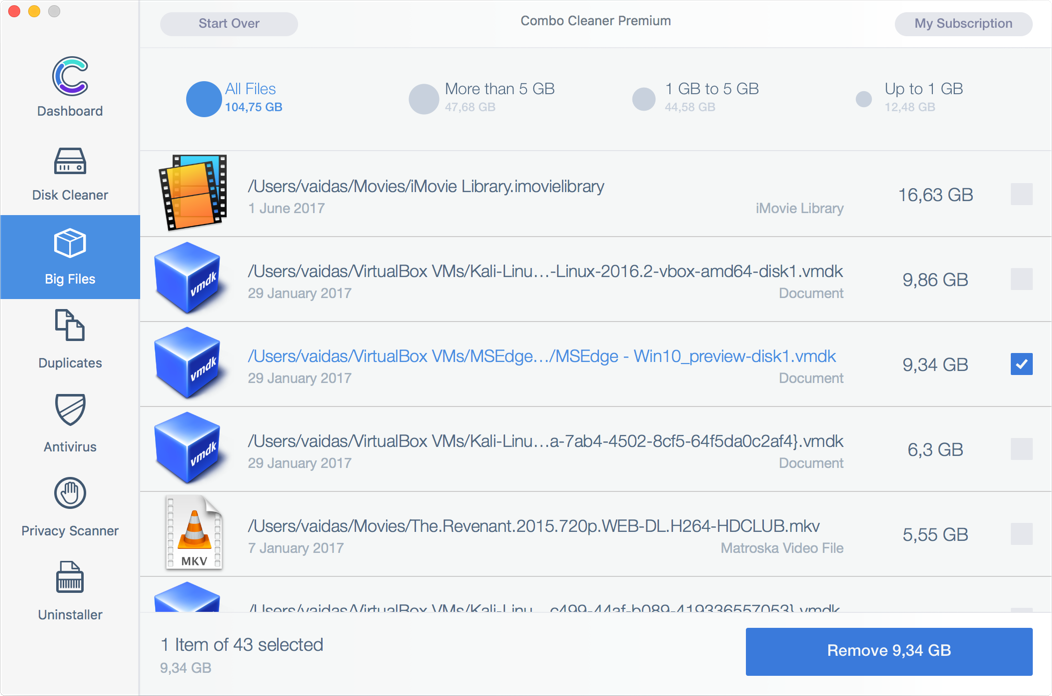
Wondering why your disk is full, but unable to locate files occupying significant disk space? Big Files Finder is free to use.
If you are wondering where all your disk space has gone, you should check your computer for large files. Most Internet users download many files (such as videos, music, and images) on a daily basis. Some of these files might be large and occupy gigabytes of disk space.
Up to 1 GB
286.5 MB
1 GB to 5 GB
4.23 GB
More than 5 GB
8.92 GB

Extremely Fast
Extremely Fast File Scan Engine. Big and Old Files Finder checks your local and external disks, immediately listing all files and folders larger than 100 megabytes (or any other user-defined size).

Easy Sorting
Large files sorted by modification date. You can also list files by creation date, thus, allowing you to determine which large files are old and perhaps redundant.
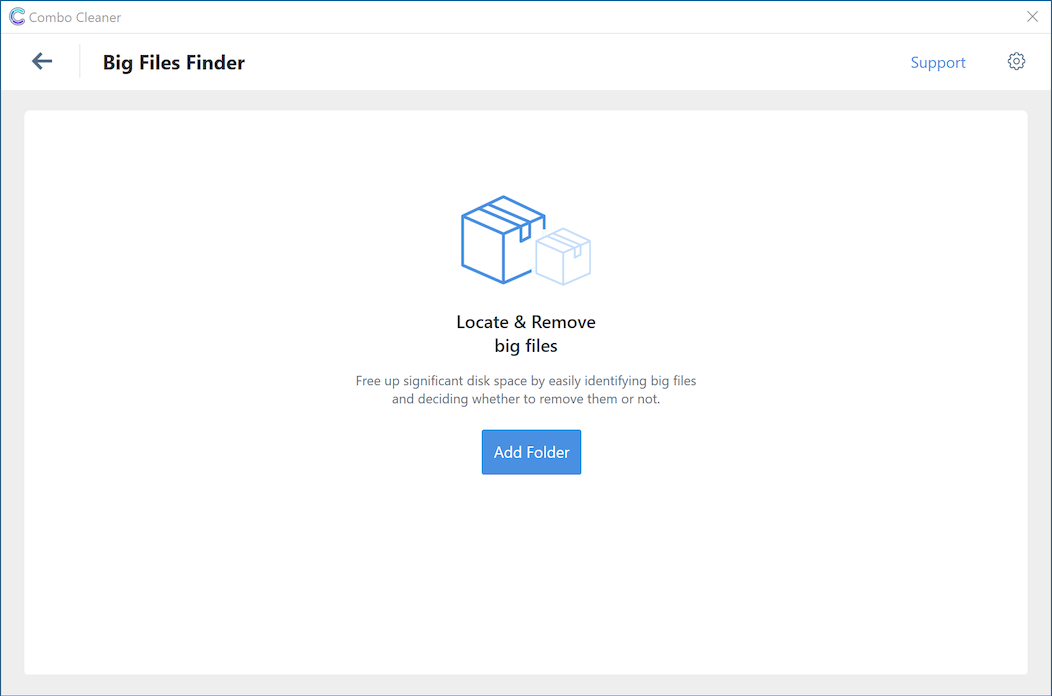
Wondering why your disk is full, but unable to locate files occupying significant disk space? Big Files Finder is free to use.
If you are wondering where all your disk space has gone, you should check your computer for large files. Most Internet users download many files (such as videos, music, and images) on a daily basis. Some of these files might be large and occupy gigabytes of disk space.
Up to 1 GB
286.5 MB
1 GB to 5 GB
4.23 GB
More than 5 GB
8.92 GB

Extremely Fast
Extremely Fast File Scan Engine. Big and Old Files Finder checks your local and external disks, immediately listing all files and folders larger than 100 megabytes (or any other user-defined size).

Easy Sorting
Large files sorted by modification date. You can also list files by creation date, thus, allowing you to determine which large files are old and perhaps redundant.
When you remove applications from your Mac, many useless, redundant files often remain on the system. Uninstaller checks for applications installed on your Mac. To uninstall applications you will have to purchase the full version of Combo Cleaner.
Combo Cleaner’s uninstaller enables you to find hidden components of applications and uninstall them from your computer. Our uninstaller delivers the quickest and easiest way to uninstall applications from your Mac, thus, resulting in extra disk space.

Logitech Camera Settings
2 items, 3.5MB available for removal

Adobe Photoshop
22 items, 500.5MB available for removal

Steam
14 items, 20.4MB available for removal

VirtualBox
154 items, 864.7MB available for removal

Files Search
Smart Associated Files Search Algorithm. Combo Cleaner will scan your installed applications and detect associated files. Often, these files are not deleted when removing the applications using the default procedures.

Smart Uninstaller
Smart app uninstaller. With just one click, you can display all installed applications in a single list. Easy file preview before removal.
What people say about us?
Contact us
Follow Combo Cleaner on Facebook to receive the latest news. We love to hear from people, please do say hello!
If you are looking for support, please use our Support Page instead.